Last updated on January 2nd, 2026 at 02:46 pm
🚀 SEO Ping Tool
Notify search engines about your website updates instantly
Enter Website URLs
Explore What’s Pinging & Free URL Ping Submission Sites List to Use in 2026
And, how you can use it and it’s ping submission sites for your website?
In computer networking, a ping is a tool used to test the connectivity between two devices on a network.
It’s like sending a little message saying “hey, are you there?” and waiting for a response.
In SEO language, marketers used to practice many SEO tools and ping submission is one of them which gives an extra boost in indexing.
In this blog, I’ll define pinging and how it works, its benefits for network operators, ping sites list and how to run a ping test.
Furthermore, I’ll explain what is considered a good ping.
Let’s dive into the details of pinging and how it can help you as a website owner.
But first, what is ping?
What is Ping Submission?
It works by sending a small packet of data to a specific network address and waiting for a response.
The time it takes for the data to travel from the sender to the recipient and back again is measured and reported as the round-trip time (RTT).
In layman’s terms, the definition of pinging looks like this:
Sending a ping and receiving a response from the recipient is called pinging.
In SEO terms, ping submission meaning is; A process of submitting your website URLs to search engines for fast crawling and indexing in SERPs.
What is Good Ping submission?
A ping response time reflects the time it takes for a data packet to travel from a computer to an Internet server and back.
However, determining what is considered a good, bad, or average ping depends on these response times. The following types of pings are commonly encountered:
- Excellent ping (less than 30ms): This type of ping is nearly undetectable and is ideal for online gaming.
- Good ping (30-50ms): Although not as fast as an excellent ping, this is still suitable for online gaming.
- Slightly slow ping (50 to 100ms): This ping is not noticeable when browsing the web but may impact gaming performance.
- Slow ping (100-500ms): This ping has little effect on web browsing, but can cause noticeable lag in online gaming.
- Very slow ping (greater than 500ms): Pings that take this long will result in significant delays for all requests.
Now, let’s dive a little deeper and understand how it works.
How Does Pinging Work?
- The sender issues an Internet Control Message Protocol (ICMP) Echo request to a specific network.
- After sending a ping command, the issuer waits for a reply from the target host.
- The target host receives the echo request and responds by sending back an echo reply packet.
Top Free Ping Submission Sites 2026
| S. No. | High PR Ping Submission Sites | Domain Authority (DA) |
|---|---|---|
| 01 | https://tools.pingdom.com/ | 84 |
| 02 | https://www.site24x7.com/ping-test.html | 57 |
| 03 | https://pingomatic.com/ | 53 |
| 04 | http://blo.gs/ping.php | 43 |
| 05 | https://pingler.com/ | 42 |
| 06 | https://totalping.com/ | 40 |
| 07 | https://feedshark.brainbliss.com/ | 35 |
| 08 | http://www.indexkings.com/ | 32 |
| 09 | http://bulklink.org/ | 25 |
| 10 | https://wmtools.me/mass-ping | 23 |
Best Sites for Ping URL for Fast Indexing
| S. No. | Ping URL for Fast Indexing | Domain Authority (DA) |
|---|---|---|
| 01 | https://feedburner.google.com/ | 92 |
| 02 | https://ping.twingly.com/ | 56 |
| 03 | http://mypagerank.net/ | 42 |
| 04 | http://www.pingfarm.com/ | 34 |
| 05 | https://infotiger.com/addurl | 32 |
| 06 | https://addurl.official.my/addurl.php | 29 |
| 07 | https://www.cleversubmitter.com/submit | 29 |
| 08 | https://www.sitesondisplay.com/add.html | 22 |
| 09 | https://www.pingmylinks.com/ | 20 |
| 10 | https://www.pingmyurls.com/ | 10 |
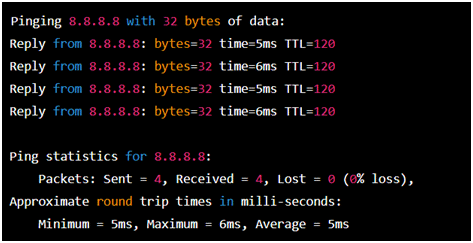
Here’s The Step-by-Step Process of a Ping
- Open the Command Prompt: Press the Windows key + R on your keyboard to open the Run dialog box, then type “cmd” and press Enter.
- Type “ping” followed by the IP address or hostname of the device you want to test connectivity to.
For example, if you want to ping Google’s DNS server at IP address 8.8.8.8, type the following command:
ping 8.8.8.8
- Press Enter. The ping utility will send several packets of data to the specified IP address and wait for a response.
- Once the ping is complete, you will see a summary of the results, including the number of packets, sent, received, and lost, as well as the average time it took for a response to be received.
Here’s the possible output might look like:
This output shows that the ping was successful, with all four packets sent and received, and an average response time of 5ms.
If any packets were lost or the response time was excessively high, it could indicate a problem with network connectivity.
How Does Pinging Helps Network Operators?
1. Testing The Connectivity
Oftentimes, a ping helps network operators to ensure that a host computer that a user is trying to reach is operating.
By sending a ping request to a device on the network, you can determine if that device is reachable and responding.
If the ping is successful, it indicates that there is connectivity between the two devices.
For this, the user can go to the command prompt screen (start/run/cmd) and enter ping xxxxx.yyy.
Here, xxxx is the second-level domain name like google and yyy is the top-level domain name like “com.”
2. Test The Speed of a Network
Pinging also helps to determine the round trip time (RTT) or latency of a ping.
The RTT or latency of a ping is the time taken to receive a response from the target host, measured in milliseconds.
The process for which the time is calculated begins as soon as the issuer sends a ping to the target host and it ends when the issuer successfully receives a response.
Usually, ping commands send multiple requests, around 4-5, in one cycle.
3. Troubleshooting Network Issues
Pinging also helps in determining the number of packets lost in the process and determining technical issues in the network.
If a ping request fails, it indicates that there is a problem with connectivity between the two devices.
A series of failed ping requests can indicate packet loss, network congestion, or routing issues, helping you identify where the problem lies.
4. Exploring The Networks Connected to a Server
One can easily utilize the ping command to identify all devices connected to a network.
As this command prompts responses from all devices on the network, it enables administrators to identify all the active connections.
Additionally, network administrators can use the ping command to regularly check the status of network devices.
This method serves as a fundamental polling technique for monitoring network devices and does not require any extra software.
Security Issues That Come With Pinging
A. Ping Spoofing
Ping spoofing is a malicious technique used by cyber attackers to deceive a network administrator into thinking that a device is active and available.
Spoofing works by altering the original ping message to fake the source of the ping and subsequently misleading the system into believing that the device is online when it is, in fact, not.
Attackers use this technique to gain unauthorized access to a network, steal sensitive information, or launch a cyber-attack.
To avoid falling victim to ping spoofing, it is crucial to maintain strict network security practices and implement network security protocols, such as firewalls and intrusion detection systems.
It is also recommended to utilize encryption tools to protect against unauthorized access and ensure that all network devices are up-to-date with the latest security patches.
B. Ping Flood
Ping flood, also known as ICMP flood, is a type of Denial of Service (DoS) attack that overwhelms a network with an excessive amount of Internet Control Message Protocol (ICMP) requests.
These requests are typically initiated by a single computer or device, with the intent of sending an enormous amount of ping messages to a targeted server, which results in network congestion and a loss of connectivity.
The ping flood attack can be prevented by implementing security measures such as firewalls and Intrusion Detection Systems (IDS), limiting the number of ICMP requests that a server will respond to.
Also, you can use load balancers to distribute traffic evenly across the network.
C. Ping Sweep
Ping sweep is a network reconnaissance technique used to scan a range of Internet Protocol (IP) addresses to determine which addresses are currently in use.
The process involves sending ICMP echo requests (pings) to a range of IP addresses within a network and then waiting for the ICMP echo reply.
If the device responds, it is considered “alive” and its IP address is recorded.
Ping sweep tools can scan large networks quickly and efficiently, enabling administrators to identify which devices are connected to the network and which are not.
Attackers also use ping sweep techniques to identify live hosts, which can then be targeted in further attacks.
Apart from using firewalls and intrusion detection systems to limit the number of ICMP requests that a server will respond to, you can also regularly scan the network to identify and address vulnerabilities.
Quick History About Pinging
The name “ping” was inspired by the sound that sonar makes when bouncing off underwater objects.
Interestingly, the name has since evolved into an acronym, standing for “Packet InterNet Groper” or “PING.”
The primary aim of this utility was to provide a simple method for testing IP network connectivity and collecting metrics related to network performance.
Remarkably, this software utility is classified as public domain, meaning that it has been freely available to use and distribute from its initial release.
The ping utility has been incredibly popular and is widely used by network administrators and engineers worldwide as a fundamental tool for troubleshooting network connectivity issues.
Conclusion
As a website owner, pinging can be a great tool for you, especially for identifying the number of web crawlers due to the backlinks you created.
A professional SEO can help you make the best use of this powerful tool and help you keep protected from malpractices.